Crippling ransomware attacks like the one that hit Garmin over the summer are becoming an all-too-common occurrence as cybercriminals get ever bolder. In Garmin’s case, the attack caused a worldwide blackout of many of its services, taking down its website, call centers, and apps — not to mention exposing its users’ sensitive personal information. Garmin reportedly paid the multimillion-dollar ransom to decrypt its data (a move that could result in regulatory penalties), but by then it had suffered great damage to its operations, brand, and reputation. Garmin’s handling of the situation was widely criticized, and as a TechRepublic article put it, “Security analysts said the situation had wide-ranging implications considering the scale of the attack, the perceived mismanagement of the initial response to the crisis, and the people behind the crime.”
I won’t speculate about what might have led to the successful attack at Garmin, but it’s a cautionary tale about the critical need to know that your data is backed up and completely secure in case you have to restore it. Basically, no one wants to take care of it, but being unprepared when it happens could be devastating. Taking steps like backing up data to its own domain, out of reach of attackers, can help lay the groundwork for a successful recovery without having to pay a ransom.
The Garmin situation also got me thinking about restoration practices, which are just as critical as the backup itself.
After decades working in enterprise backup and recovery, I’ve noticed that data managers tend to grant restoration access too freely to people who don’t understand the data they are trying to recover. Often, it’s because the managers are looking for a way to make things easier. (And who can blame them? Managing enterprise data backup is tough stuff.) But if it becomes too easy and too accessible, it can mean there’s not enough control over a complex environment. You can miss the appropriate checks and balances in who has access to data recovery, which could be disastrous for the business.
Best practices in data restoration
To avoid such disasters, follow a few simple best practices to ensure that secure recoveries are possible.
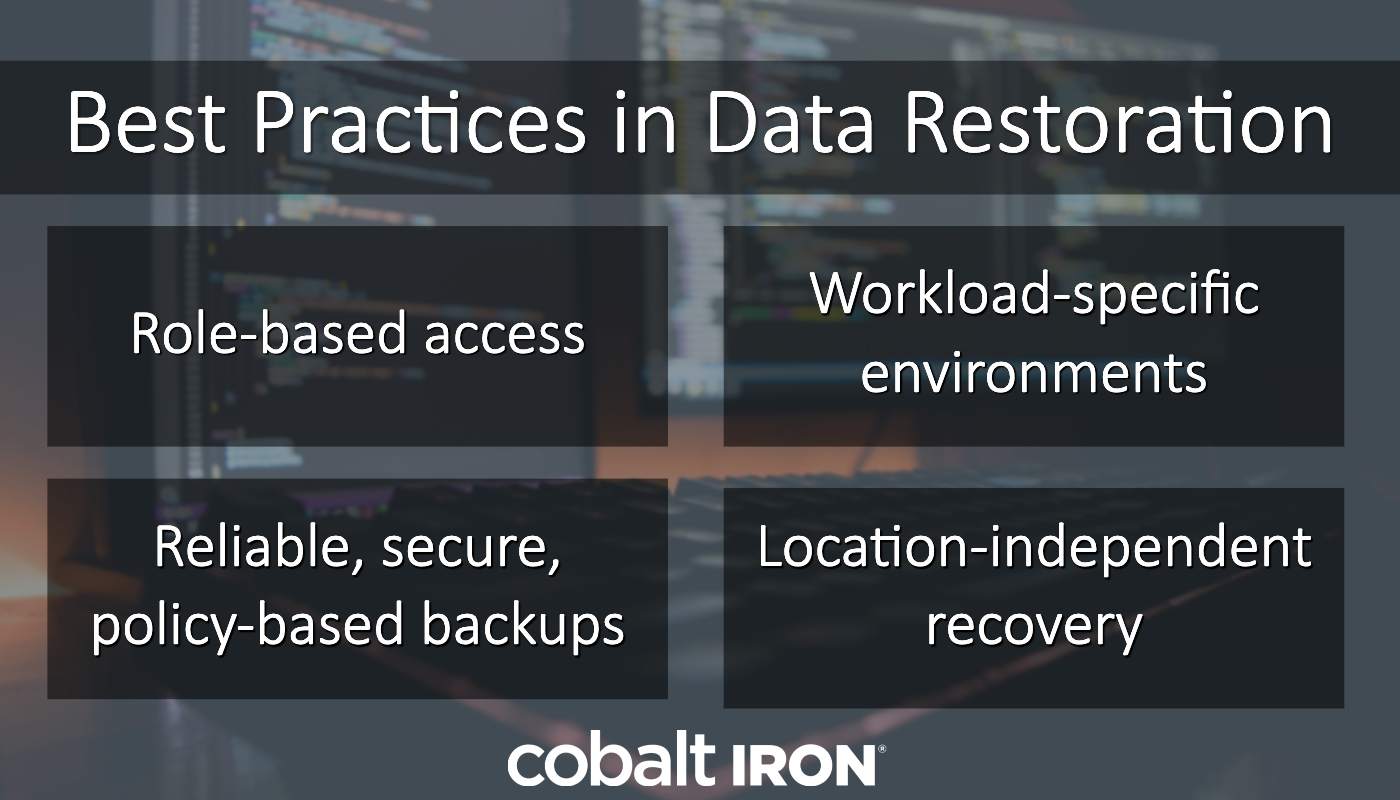
Role-based access
One of the first things you can do to secure your backup and recovery operation is to implement role-based access controls, which make it so that data owners can access and recover only the data they need and nothing else.
Why does role-based access matter? Because it demonstrates that your organization has reached a level of maturity with your security practices and shows you’re already thinking in terms of keeping data owners responsible for the data they use. This level of maturity is necessary in today’s world, especially considering that backups are now a regular target of ransomware attacks.
Role-based access controls also minimize the potential negatives of a faulty restore by someone who isn’t familiar with the data. Recovering too much could overwrite more current or correct data. Recovering too little doesn’t solve the issue. Recovering to the wrong location could make the data unusable, unavailable, or inappropriately accessible. Data owners know the data they’re dealing with, where it needs to go, and how much of it needs to be restored. Consider the role of the database administrator, for example. Database admins are uniquely qualified to understand the architecture of the database. When a recovery is needed, they will be able to pull just the right amount of data for restoration and know just where it should be restored.
Workload-specific environments
This concept goes hand in hand with role-based access. It’s the idea that you keep administrators in the right environment for the right task. To that end, make sure your backup and restore solution allows admins to perform recoveries either through workload-specific interfaces or through plug-ins based on commercially available technology. The solution should be integrated with application management interfaces, giving each team the access and data protection tools they need wherever they need them.
With this approach, administrators stay where they need to be to get their jobs done while ensuring security across the enterprise. Restores are executed by administrators, application owners, and users as needed, ensuring full security and access control depending on the business requirements and the location of the data.
Reliable, secure, policy-based backups
In order to restore data, you must ensure consistent, usable backups are continually performed. Look for a solution with a centralized interface that guarantees adherence to data protection business policies. You probably have multiple specialized teams managing separate tasks across the enterprise. When mission-critical restore needs arise, you need to know that your business can restore its data. Monitored, policy-based backups can give you this assurance.
Likewise, backup administration and daily management should either be software-automated or executed from a central web application. And policy management and reporting should be easy to visualize and customize through that same interface. These practices all help ensure smoother, successful recoveries.
Location-independent recovery
Make sure restoration can happen from any location (on-premises, remote, mobile, in the cloud, across clouds).
The Cobalt Iron Compass data protection platform follows all of those best practices. After years of working with enterprise customers that manage legacy tools, specialized teams, and separation of duties, Cobalt Iron understands the unique requirements that enterprises face when protecting and recovering data. Based on this experience, we designed Compass to optimize interfaces around simplicity and familiarity for application and data owners and administrators. These interfaces, coupled with a unique orchestration of commercially available technology plug-ins, are just two reasons why Compass has industry-leading restore capabilities for the broadest range of workloads in the market.
The moral of the story: Lay the groundwork now for data restoration should you ever need to do it. And take the time to establish effective backup policies and grant the appropriate access and recovery rights. So if the time comes, you can thwart attacks and get back to business unscathed.
< Back to Blog
