You know what they say about chains: They’re only as strong as their weakest link. And when it comes to data security, the integrity of each link can spell the difference between solid business continuity and a malware disaster.
As a Lenovo On Demand partner, Cobalt Iron is delivering all of the benefits of the Compass best-of-breed enterprise Software-as-a-Service data protection platform to Lenovo’s data center customers. In simple terms, it means that enterprises running Lenovo servers are able to achieve the industry’s best practices for data protection in one seamless, integrated solution.
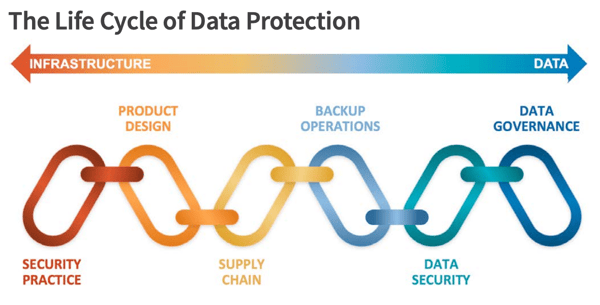
It’s useful to look at the Lenovo-Compass partnership – and the value it brings to joint customers – as a lifecycle continuum from infrastructure development to data, with each link representing a vital component of a comprehensive data protection chain (see below). In this model, Lenovo covers the security discipline of the infrastructure portion, with Compass software taking the security lead on the data and operational sides.
How to ensure data security across the data protection lifecycle
Start Product development with Security Practices in mind
The data protection lifecycle starts with Security Practices — provided through Lenovo’s advanced security training, software security review board, and diligently protected source code. In addition, Lenovo’s transparent security development processes are reviewed and approved by the U.S. government, and Lenovo follows rigid and robust vulnerability management practices.
Include Security in Product Design
Lenovo builds standards-based security into its Product Design, ensuring its servers won’t introduce security vulnerabilities at a hardware level. Design practices include a secure software development lifecycle, ongoing product security assessments and penetration testing, blocking unauthorized firmware, and an innovative, tamper-proof design.
Lockdown the supply chain
Lenovo’s secure Supply Chain protects servers from unauthorized entry at any point in the manufacturing process. In fact, Lenovo has achieved the highest security level based on supply chain audits by U.S. government authorities.
Automate Backup Operations with Software
Compass takes over at the Backup Operations phase, protecting backup data and operations with the industry’s most comprehensive and rigorous security practices. Compass backup operations cover all activities involved in the deployment, operation, upkeep, and management of the backup solution.
Ensure Data Security with Access Controls
As a SaaS solution, Compass delivers award-winning, end-to-end Data Security without additional licenses or costs. Compass’ built-in Cyber Shield technology delivers industry-standard security features such as immutability, completely restricted access to backup data, backup containment and isolation by design, integration with directory and multifactor authentication solutions, and data encryption in flight and at rest, and automatic data validation during ingest and restore.
Implement and Maintain Strict Data Governance
Compass Cyber Shield covers the final link in the chain, Data Governance, with a system for defining who within an organization has authority and control over data assets and how those data assets may be used. Data Governance encompasses the people, processes, and technologies required to manage and protect data assets. The Compass solution adds analytics to the governance process to provide deeper insight into the backup data.
These elements link together to form a complete Chain of Trust, strengthened by the robust security practices of two industry leaders: Lenovo and Cobalt Iron. The result is a security strategy that covers the entire data protection lifecycle in a simple-to-deploy and easy-to-manage solution.
Learn more in this free on-demand webinar:
< Back to Blog